Viruses and worms are often used interchangeably: there are a few key differences in how they work. Both viruses and worms are a type of malware: a worm is a type of virus.
Discover your weak points and strengthen your resilience: Run a Free Ransomware Readiness Test
What is a Computer Virus?
Computer viruses are named after human viruses that spread from person to person. A computer virus is a program made of malicious code that can propagate itself from device to device. Like a cold that alters your well-being, when your computer is infected, it alters the way your computer operates, can destroy your files, or prevent it from working altogether.
Learn ransomware fundamentals now with our free course.
A virus typically attaches itself to a program, file, or the boot sector of the hard drive. Once the virus attaches itself to that file or program (aka, the host), they’re infected.
When the infected application or file runs in the computer, the virus activates and executes in the system. It continues to replicate and spread by attaching replicas of itself to other files and applications in the system.
How Does a Computer Virus Spread?
A virus spreads when the infected file or program migrates through networks, file collaboration apps, email attachments, and USB drives. Once a user opens the infected file or program, the vicious cycle repeats itself all over again.
Typically, the host program continues to function after the viral infection, but some viruses overwrite entire programs with copies of themselves, which corrupts and destroys the host program altogether. Viruses can also attack data: they can disrupt access, corrupt, and/or destroy your data.
What’s a Computer Worm?
Worms are a self-replicating type of malware (and a type of virus) that enter networks by exploiting vulnerabilities, moving quickly from one computer to another. Because of this, worms can propagate themselves and spread very quickly – not only locally, but have the potential to disrupt systems worldwide.
Unlike a typical virus, worms don’t attach to a file or program. Instead, they slither and enter computers through a vulnerability in the network, self-replicating and spreading before you’re able to remove the worm. But by then, they’ll already have consumed all the bandwidth of the network, interrupting and arresting large network and web servers.
A Modern Computer Worm Story
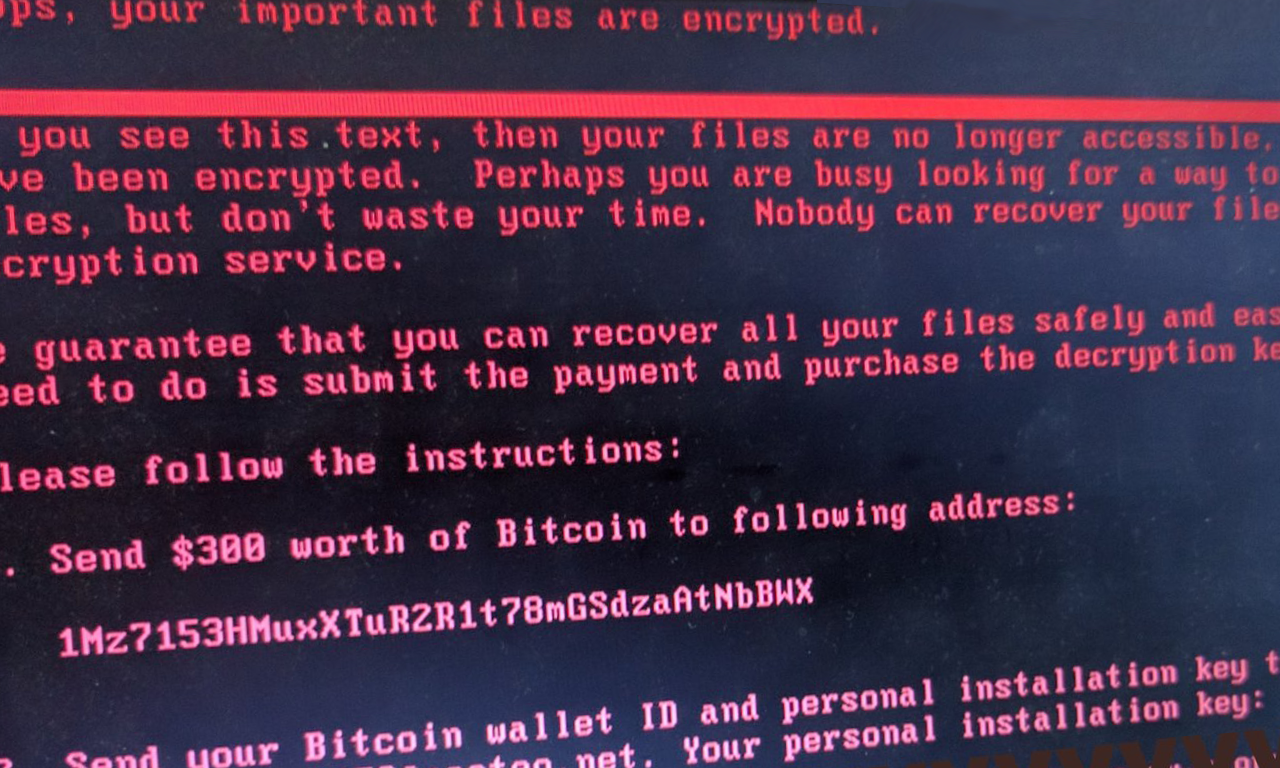
In 2017, the WannaCry worm attack caused damage worth hundreds of millions to billions of dollars. Also known as WannaCry ransomware, this attack is a hybrid of ransomware and a worm – specifically cryptoworm.
Ransomware is a type of malware that holds a user’s data hostage: it encrypts data and asks the victim to pay a ransom, betting on the user’s willingness to pay to restore the user’s data. Ransomware infections often occur through phishing campaigns.
Instead, WannaCry took advantage of a vulnerability in Microsoft’s SMB Version 1 file sharing protocol, typically used by Windows machines to communicate with file systems over a network. Those who didn’t patch SMB Version 1 learned the hard way about the perils of forgetting to patch their systems.
WannaCry leveraged EternalBlue, a Windows SMB protocol exploit, to gain access, install a backdoor, and download software – infecting the systems.
In short, WannaCry self-propagated, self-replicated, and quickly traversed entire networks, causing worldwide damage.
How to Protect Yourself from Computer Viruses and Computer Worms
Here are some simple ways to protect yourself:
- Install anti-virus software and firewall
- Track potential data exfiltration at the edge and attacks at the point of entry
- Remember to regularly install security patches
- Monitor and analyze file and user behavior
- Leverage security analytics to spot suspicious behavior
- Set up alerts to notify you automatically and immediately when an anomaly occurs
How Varonis Helps
When a virus or worm evades your anti-virus detection software or endpoint to exfilitrate your organization’s data, Varonis can help.
Varonis DatAdvantage monitors and analyzes file and email activity – as well as user behavior. When there’s an unusual amount of lockouts that occur or a thousand files are opened in a minute, Varonis DatAlert can detect these anomalies, automate security responses, and enable teams to investigate security incidents directly in the web UI. Varonis Edge adds context with perimeter telemetry, detecting signs of attack at the perimeter via DNS, VPN, and Web Proxies.
Discover how Varonis can help defend against worms and viruses – see Varonis in action with a 1:1 demo today.
What should I do now?
Below are three ways you can continue your journey to reduce data risk at your company:
Schedule a demo with us to see Varonis in action. We'll personalize the session to your org's data security needs and answer any questions.
See a sample of our Data Risk Assessment and learn the risks that could be lingering in your environment. Varonis' DRA is completely free and offers a clear path to automated remediation.
Follow us on LinkedIn, YouTube, and X (Twitter) for bite-sized insights on all things data security, including DSPM, threat detection, AI security, and more.