-
 Data Security
Data SecuritySep 16, 2014
Phishing Attacks Classified: Big Phish vs. Little Phishes
The CMU CERT team I referred to in my last post also has some interesting analysis on the actual mechanics of these phishing attacks. Based on reviewing their incident database, the...

Michael Buckbee
1 min read
-
 Data Security
Data SecuritySep 05, 2014
In Search of Kerberos’s Golden Ticket
In a Kerberos environment, all users get tickets, or more specifically TGTs (Ticketing Granting Tickets). It’s the starting point for gaining access to services—network files, email, apps, etc. In Windows,...

Michael Buckbee
2 min read
-
 Data Security
Data SecurityAug 27, 2014
Kerberos Weaknesses: Pass the Ticket Is a Real Threat
August is always a good time to check up on the dark side. Black Hat had its annual conference earlier this month, and there are always presentations worth looking at....

Michael Buckbee
2 min read
-
 Data Security
Data SecurityAug 11, 2014
Top Five Most Dangerous Software Errors
Over the years, Mitre, the MIT research group, has been analyzing software bugs and missteps that hackers have been able to exploit. Their Common Vulnerabilities and Exposures (CVE) classifications are...

Michael Buckbee
3 min read
-
 Data Security
Data SecurityJul 15, 2014
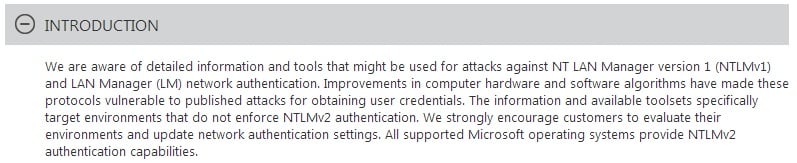
Pass the Hash, Part III: How NTLM Will Get You Hacked
The most important takeaway about PtH is that the password hashes that are stored in memory (and grabbed by hackers) are a feature of Single Sign On.

Michael Buckbee
4 min read
-
 Data Security
Data SecurityJul 08, 2014
3 Deadly File Permissions Mistakes
Scarily, in most organizations people have access to much more information than they need in order to do their jobs. With file permissions, it’s easy to mess things up and...

Rob Sobers
2 min read
-
 Data Security
Data SecurityJun 26, 2014
A Closer Look at Pass the Hash, Part II: Prevention
Last week, I attended a webinar that was intended to give IT attendees a snapshot of recent threats—a kind of hacker heads-up. For their representative case, the two sec gurus...

Michael Buckbee
3 min read
-
 Data Security
Data SecurityJun 17, 2014
A Closer Look at Pass the Hash, Part I
We’ve done a lot of blogging at the Metadata Era warning you about basic attacks against passwords. These can be mitigated by enforcing strong passwords, eliminating vendor defaults, and enabling...

Michael Buckbee
3 min read
-
 Data Security
Data SecurityMay 21, 2014
What’s the Difference between Hacking and Phishing?
Because I’ve boldly assigned myself the task to explain hacking and phishing, I feel compelled to define both terms concisely because, as Einstein’s been quoted countless times, “If you can’t...

Michael Buckbee
2 min read
-
 Data Security
Data SecurityApr 21, 2014
How to Configure Varonis and EMC Isilon
Customers of EMC’s popular Isilon storage platform have been clamoring for sophisticated controls around their sensitive, regulated content—e.g., SOX, PCI, intellectual property, etc. Varonis is the perfect fit. With our...

Rob Sobers
1 min read
-
 Data Security
Data SecurityMar 11, 2014
5 Privacy Concerns about Wearable Technology
With over 55 different fitness wearable devices to choose from, the wearables market has breathed new life into our personal health, providing us with more insight into our sleep patterns,...

Michael Buckbee
3 min read
-
 Data Security
Data SecurityMar 05, 2014
Automate Exchange Distribution List Management
From a business perspective, distribution lists (DLs) for email communications are a powerful and well-understood concept in IT. And they are popular: Exchange admins have voted with their right-clicks, creating...

Michael Buckbee
2 min read
SECURITY STACK NEWSLETTER
Ready to see the #1 Data Security Platform in action?
Ready to see the #1 Data Security Platform in action?
“I was amazed by how quickly Varonis was able to classify data and uncover potential data exposures during the free assessment. It was truly eye-opening.”
Michael Smith, CISO, HKS
"What I like about Varonis is that they come from a data-centric place. Other products protect the infrastructure, but they do nothing to protect your most precious commodity — your data."
Deborah Haworth, Director of Information Security, Penguin Random House
“Varonis’ support is unprecedented, and their team continues to evolve and improve their products to align with the rapid pace of industry evolution.”
Al Faella, CTO, Prospect Capital