-
 Data Security
Data SecurityJun 06, 2017
Reality Leah Winner and the Age of Insider Threats
Prosecutors allege that 25-year-old federal contractor Reality Leah Winner printed a top-secret NSA document detailing the ongoing investigation into Russian election hacking last November and mailed it to The Intercept....

Rob Sobers
2 min read
-
 Data Security
Data SecurityJun 06, 2017
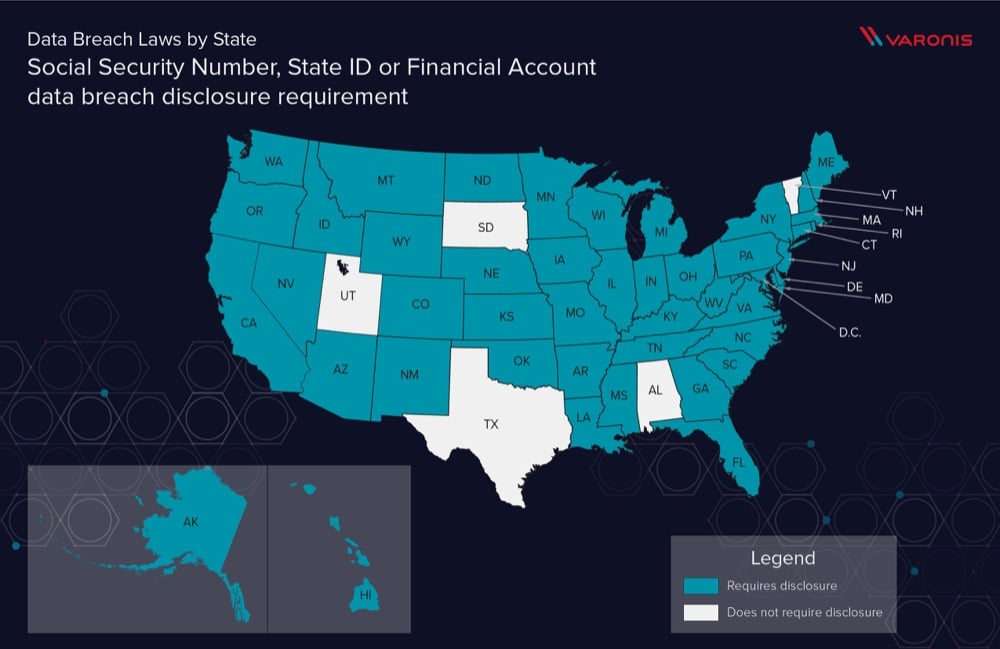
Data Breach Definition by State
State governments are becoming more aware of PII and PHI data breaches, how about your state? See how PII is protected per state with our primer on US State Data Breach Law Definitions.

Michael Buckbee
10 min read
-
 Data Security PowerShell
Data Security PowerShellJun 02, 2017
Disabling PowerShell and Other Malware Nuisances, Part II
Whitelisting apps is nobody’s idea of fun. You need to start with a blank slate, and then carefully add back apps you know to be essential and non-threatening. That’s the...

Michael Buckbee
3 min read
-
 Data Security
Data SecurityMay 26, 2017
Disabling PowerShell and Other Malware Nuisances, Part I
Back in more innocent times, circa 2015, we began to hear about hackers going malware-free and “living off the land.” They used whatever garden-variety IT tools were lying around on...

Michael Buckbee
4 min read
-
 Data Security
Data SecurityMay 22, 2017
Is a ransomware attack a data breach?
Understanding if ransomware is a data breach is vital to determining what response your IT and Legal department needs to take.

Michael Buckbee
1 min read
-
 Data Security
Data SecurityMay 20, 2017
EternalRocks leaves backdoor trojan for remote access to infected machines
What we know so far The WannaCry ransomware worm outbreak from last Friday week used just one of the leaked NSA exploit tools, ETERNALBLUE, which exploits vulnerabilities in the SMBv1...

Kieran Laffan
2 min read
-
 Data Security
Data SecurityMay 17, 2017
Adylkuzz: How WannaCry Ransomware Attack Alerted The World To Even Worse Threats
Your garden variety ransomware, like Cerber, is the canary in the coal mine that rudely, but thankfully announces bigger security issues: insider threats and cyberattacks that take advantage of too...

Rachel Hunt
2 min read
-
 Data Security
Data SecurityMay 15, 2017
Why did last Friday's ransomware infection spread globally so fast?
Ransomware is a type of malware that encrypts your data and asks for you to pay a ransom to restore access to your files. Cyber criminals usually request that the...

Kieran Laffan
3 min read
-
 Data Security
Data SecurityMay 12, 2017
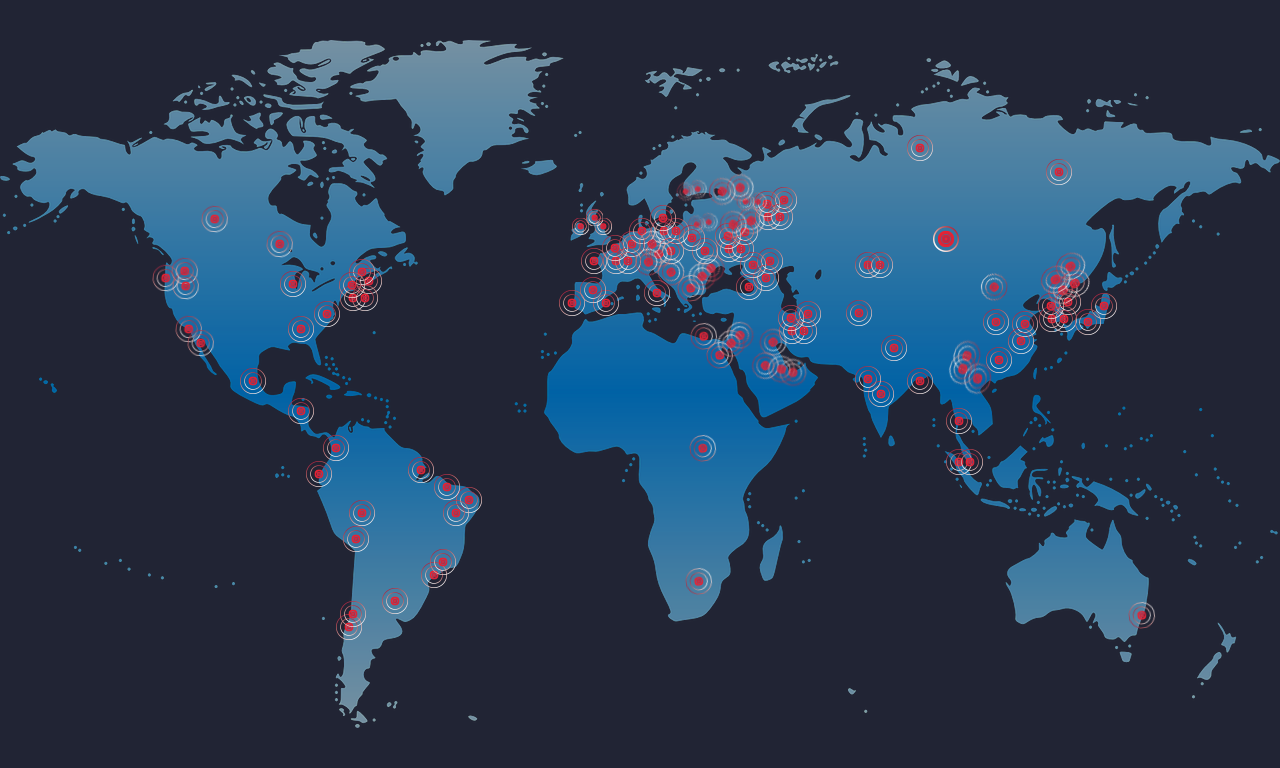
🚨 Massive Ransomware Outbreak: What You Need To Know
Remember those NSA exploits that got leaked a few months back? A new variant of ransomware using those exploits is spreading quickly across the world – affecting everyone from the...

Michael Buckbee
2 min read
-
 Data Security
Data SecurityMay 12, 2017
Planet Ransomware
If you were expecting a quiet Friday in terms of cyberattacks, this ain’t it. There are reports of a massive ransomware attack affecting computers on a global scale: in the...

Michael Buckbee
1 min read
-
 Data Security
Data SecurityApr 12, 2017
What is a Data Security Portfolio?
A Data Security Platform (DSP) is a category of security products that replaces traditionally disparate security tools to reduce risk and prevent threats.

Rob Sobers
6 min read
-
 Data Security
Data SecurityApr 11, 2017
Varonis Data Security Platform Listed in Gartner 2017 Market Guide for Data-Centric Audit and Protection
In 2005, our founders had a vision to build a solution focused on protecting the data organizations have the most of and yet know the least about – files and...

Rachel Hunt
1 min read
SECURITY STACK NEWSLETTER
Ready to see the #1 Data Security Platform in action?
Ready to see the #1 Data Security Platform in action?
“I was amazed by how quickly Varonis was able to classify data and uncover potential data exposures during the free assessment. It was truly eye-opening.”
Michael Smith, CISO, HKS
"What I like about Varonis is that they come from a data-centric place. Other products protect the infrastructure, but they do nothing to protect your most precious commodity — your data."
Deborah Haworth, Director of Information Security, Penguin Random House
“Varonis’ support is unprecedented, and their team continues to evolve and improve their products to align with the rapid pace of industry evolution.”
Al Faella, CTO, Prospect Capital