-
 Data Security
Data SecurityMar 01, 2018
GDPR Data Protection Supervisory Authority Listing
The DPA (Data Protection Authority) is the agency within each European Union country that is responsible for GDPR (General Data Protection Regulation) assistance and enforcement. A Data Protection Authority handles...

Michael Buckbee
5 min read
-
 Data Security
Data SecurityDec 15, 2017
Best of the Inside Out Security Show Podcast
We’ve interviewed many privacy experts, chief data officers, security pros and learned so much about the real world. Because we’ve covered so much, I’ve curated the most popular infosec quotes...

Michael Buckbee
1 min read
-
 Data Security
Data SecurityOct 30, 2017
Why A Honeypot Is Not A Comprehensive Security Solution
A core security principle and perhaps one of the most important lessons you’ll learn as a security pro is AHAT, “always have an audit trail”. Why? If you’re ever faced...

Michael Buckbee
5 min read
-
 Data Security
Data SecurityOct 03, 2017
[Transcript] Ofer Shezaf and Keeping Ahead of the Hackers
Inside Out Security: Today I’m with Ofer Shezaf, who is Varonis’s Cyber Security Director. What does that title mean? Essentially, Ofer’s here to make sure that our products help customers...

Michael Buckbee
11 min read
-
 Data Security
Data SecurityJun 28, 2017
Complete Guide to Windows File System Auditing - Varonis
Windows file auditing is key in a cybersecurity plan. Learn about file system auditing and why you'll need an alternate method to get usable file audit data

Michael Buckbee
7 min read
-
 Data Security
Data SecurityJun 26, 2017
What is UPnP and why is it Dangerous?
Learn what UPnP (Universal Plug and Play) is and about its potential dangers. Contact us today for all of your cybersecurity needs.

Michael Buckbee
3 min read
-
 Data Security
Data SecurityJun 20, 2017
I Click Therefore I Exist: Disturbing Research On Phishing
Homo sapiens click on links in clunky, non-personalized phish mails. They just do. We’ve seen research suggesting a small percentage are simply wired to click during their online interactions. Until...

Michael Buckbee
3 min read
-
 Data Security
Data SecurityJun 06, 2017
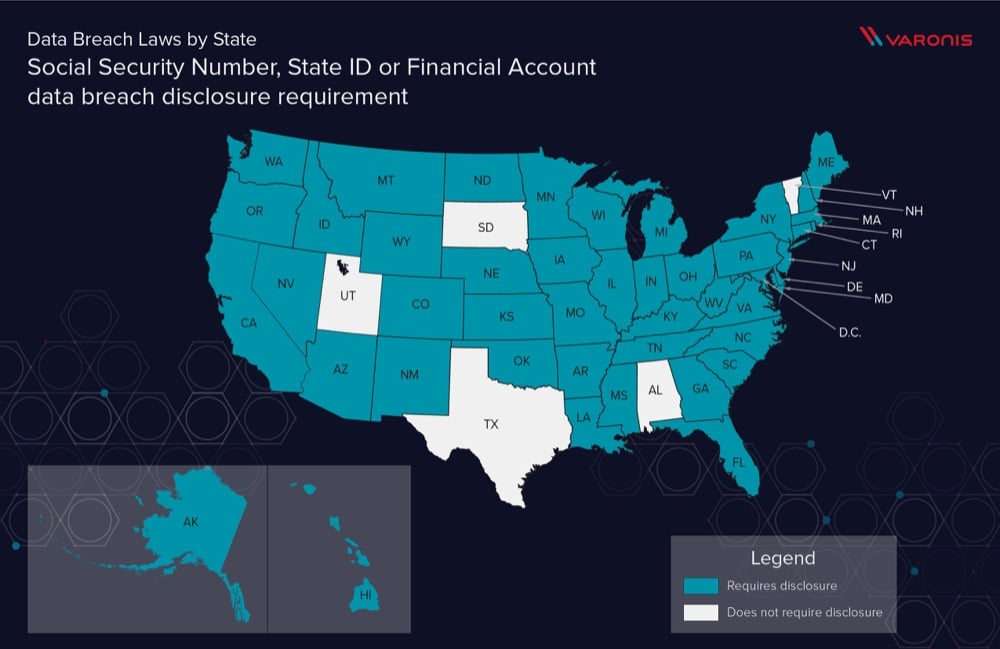
Data Breach Definition by State
State governments are becoming more aware of PII and PHI data breaches, how about your state? See how PII is protected per state with our primer on US State Data Breach Law Definitions.

Michael Buckbee
10 min read
-
 Data Security
Data SecurityMay 26, 2017
Disabling PowerShell and Other Malware Nuisances, Part I
Back in more innocent times, circa 2015, we began to hear about hackers going malware-free and “living off the land.” They used whatever garden-variety IT tools were lying around on...

Michael Buckbee
4 min read
-
 Data Security
Data SecurityMay 20, 2017
EternalRocks leaves backdoor trojan for remote access to infected machines
What we know so far The WannaCry ransomware worm outbreak from last Friday week used just one of the leaked NSA exploit tools, ETERNALBLUE, which exploits vulnerabilities in the SMBv1...

Kieran Laffan
2 min read
-
 Data Security
Data SecurityMay 15, 2017
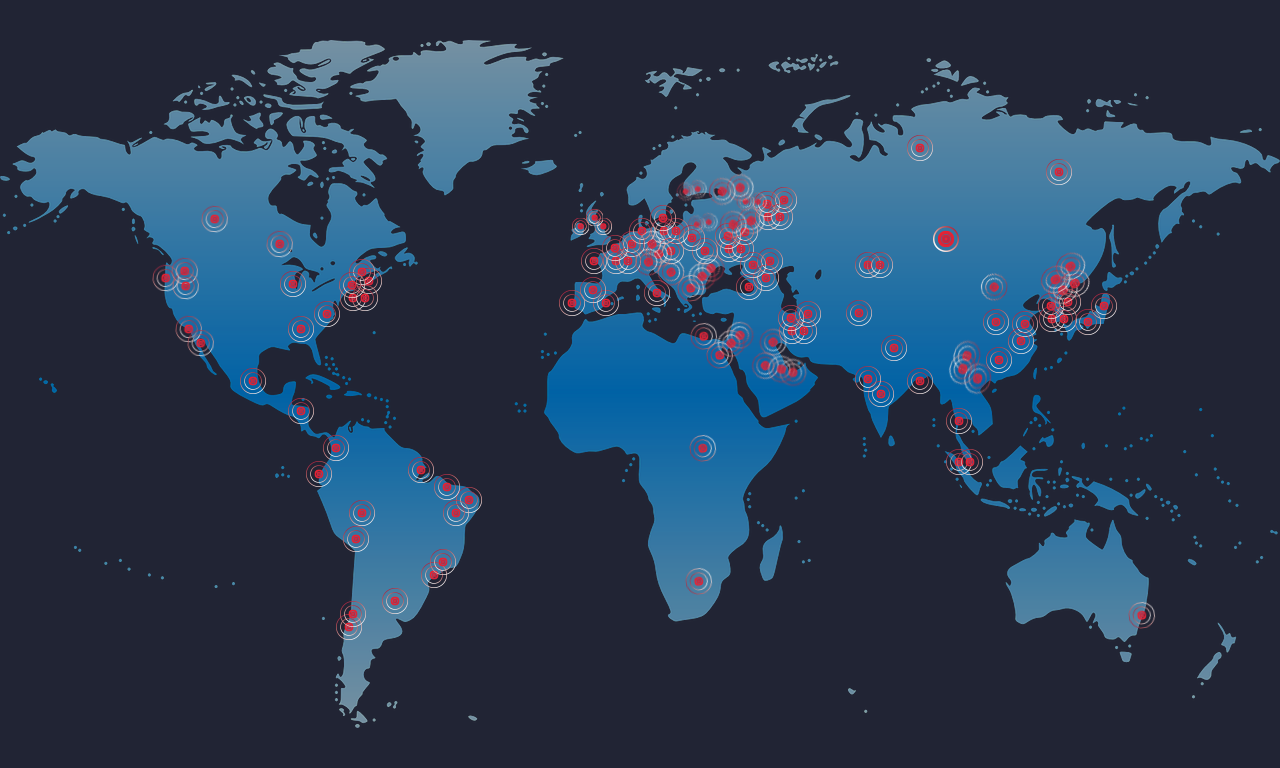
Why did last Friday's ransomware infection spread globally so fast?
Ransomware is a type of malware that encrypts your data and asks for you to pay a ransom to restore access to your files. Cyber criminals usually request that the...

Kieran Laffan
3 min read
-
 Data Security
Data SecurityMay 12, 2017
🚨 Massive Ransomware Outbreak: What You Need To Know
Remember those NSA exploits that got leaked a few months back? A new variant of ransomware using those exploits is spreading quickly across the world – affecting everyone from the...

Michael Buckbee
2 min read
SECURITY STACK NEWSLETTER
Ready to see the #1 Data Security Platform in action?
Ready to see the #1 Data Security Platform in action?
“I was amazed by how quickly Varonis was able to classify data and uncover potential data exposures during the free assessment. It was truly eye-opening.”
Michael Smith, CISO, HKS
"What I like about Varonis is that they come from a data-centric place. Other products protect the infrastructure, but they do nothing to protect your most precious commodity — your data."
Deborah Haworth, Director of Information Security, Penguin Random House
“Varonis’ support is unprecedented, and their team continues to evolve and improve their products to align with the rapid pace of industry evolution.”
Al Faella, CTO, Prospect Capital