-
 Data Security
Data SecurityJun 17, 2020
MITRE ATT&CK Framework: Everything You Need to Know
The MITRE ATT&CK matrices are an invaluable resource for cybersecurity pros. Read on to learn more about ATT&CK tactics and techniques.

Michael Buckbee
6 min read
-
 Data Security Security Bulletins
Data Security Security BulletinsJun 17, 2020
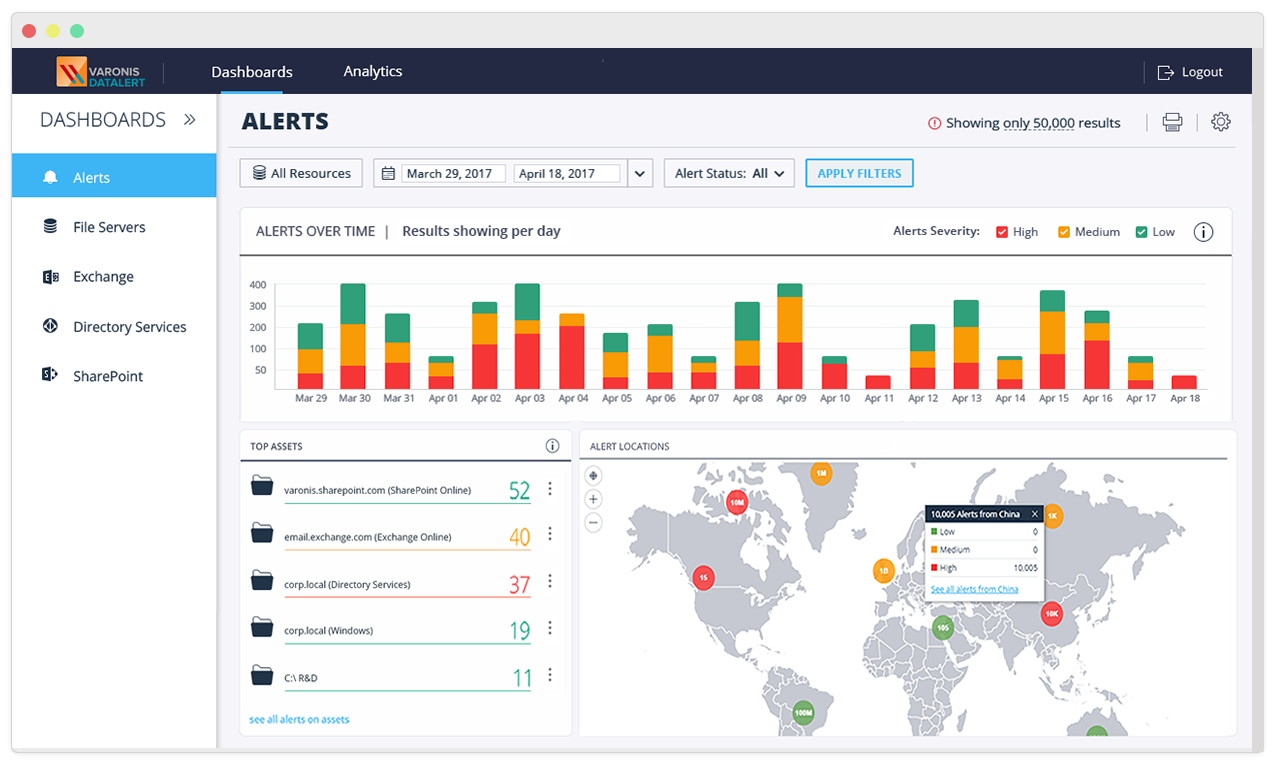
Introducing Varonis Data Security Platform 6.4.100: Varonis Edge, GDPR Threat Models, Geolocation and More
It’s the beginning of a new year, and we have a huge new beta release to share with you. The beta release of the Varonis Data Security Platform 6.4.100 dropped...

Michael Buckbee
1 min read
-
 Data Security
Data SecurityJun 17, 2020
How To Prevent Ransomware: The Basics
Ransomware is a destructive type of malware that has taken down city governments and cost organization millions. Learn more about how to prevent ransomware

Michael Buckbee
12 min read
-
 Active Directory Data Security
Active Directory Data SecurityJun 17, 2020
7 Key Risk Indicators in the Varonis Active Directory Dashboard
All an attacker needs is time and motivation to infiltrate your network. It’s your job to make their efforts to break in and remain undetected as difficult as possible. First,...

Michael Buckbee
6 min read
-
 Data Security
Data SecurityJun 17, 2020
12 Most Disregarded Cybersecurity Tasks
It is important that cybersecurity be prioritized by every level of individual in an organization. We're going over tips to follow to manage risk today.

Rob Sobers
1 min read
-
 Data Security
Data SecurityJun 17, 2020
What is OSINT?
Open source intelligence is often utilized by hackers and red teams to leverage public data while conducting investigations, often using database searches.

Kody Kinzie
8 min read
-
 Data Security
Data SecurityJun 17, 2020
What is a Rootkit? How Can You Detect it?
Think there might be a chance you caught a rootkit virus? Learn more about these toolboxes of the malware world and just how to detect them with our guide.

Michael Buckbee
3 min read
-
 Data Security
Data SecurityJun 17, 2020
Is Your Biggest Security Threat Already Inside Your Organization?
Is your company protected against insider threats? From malicious ex-employees to negligent staff, your biggest cybersecurity concern may already be inside.

Rob Sobers
1 min read
-
 Data Security
Data SecurityJun 17, 2020
Ransomware Meets Its Match With Automated Cyber Defenses
The “good news” about hacking is that while leaving you with potentially enormous incident response costs — customer notifications, legal fees, credit monitoring, class-action suits — your business can still...

Michael Buckbee
5 min read
-
 Data Security
Data SecurityJun 17, 2020
Insider Threats: Stealthy Password Hacking With Smbexec
As we’ve been writing about forever, hackers are relying more on malware-free techniques to fly below the radar. They’re using standard Windows software to live off the land, thereby getting...

Michael Buckbee
6 min read
-
 Data Security
Data SecurityJun 17, 2020
Americans and Privacy Concerns: Who Do We Trust?
Who do Americans trust with their personal information? We surveyed 1,000 people to see who America puts their trist in the most.

Rob Sobers
4 min read
-
 Data Security Security Bulletins
Data Security Security BulletinsJun 17, 2020
Varonis DataPrivilege and RSA® Identity Governance and Lifecycle
We’re thrilled to announce interoperability between Varonis DataPrivilege and RSA® Identity Governance and Lifecycle, with a new Implementation Blueprint. This Implementation Blueprint will help the business to quickly detect security...

Michael Buckbee
1 min read
SECURITY STACK NEWSLETTER
Ready to see the #1 Data Security Platform in action?
Ready to see the #1 Data Security Platform in action?
“I was amazed by how quickly Varonis was able to classify data and uncover potential data exposures during the free assessment. It was truly eye-opening.”
Michael Smith, CISO, HKS
"What I like about Varonis is that they come from a data-centric place. Other products protect the infrastructure, but they do nothing to protect your most precious commodity — your data."
Deborah Haworth, Director of Information Security, Penguin Random House
“Varonis’ support is unprecedented, and their team continues to evolve and improve their products to align with the rapid pace of industry evolution.”
Al Faella, CTO, Prospect Capital