-
 Data Security PowerShell Security Bulletins
Data Security PowerShell Security BulletinsMar 08, 2021
How to Merge in Git: Remote and Local Git Repositories Tutorial
Follow this PowerShell Git tutorial on how to merge in Git, meaning how to take a local repository and merge it into a remote repository.

Jeff Brown
6 min read
-
 Data Security
Data SecurityMar 02, 2021
Attack lab: Spear Phishing with Google Drive Sharing
Follow along as we show you how scammers are spear phishing with Google Drive sharing to avoid traditonal SPAM filters in Gmail that catch their scams

Nathan Coppinger
4 min read
-
 Data Security
Data SecurityFeb 25, 2021
Varonis Veterans Spotlight: Georgi Georgiev
Welcome to the Varonis Veteran Spotlight! The purpose of this spotlight is to show our gratitude and appreciation for our Varonis Veterans, as well as honor their military service and...

Belinda Ng
4 min read
-
 Data Security
Data SecurityFeb 22, 2021
Your Primer to Third-Party Risk Management
Learn the basics, definitions and best practices of third-party risk management

Josue Ledesma
6 min read
-
 Data Security PowerShell Security Bulletins
Data Security PowerShell Security BulletinsFeb 22, 2021
Watch: ReConnect - Version 8.5 and Combating Insider Risks in Microsoft 365
Kilian and Brian walk through the TL;DR version of our Varonis 8.5 and combatting insider risks in Microsoft 365 event. They cover the high-level points, and answer the best questions during the event.

Kilian Englert
1 min read
-
 Active Directory Data Security
Active Directory Data SecurityFeb 19, 2021
Group Policy Editor Guide: Access Options and How to Use
Group Policy Editor (gpedit) is an important part of the Active Directory system administrator’s toolkit. Read this blog for more details about gpedit.

Michael Buckbee
4 min read
-
 Data Security Threat Research
Data Security Threat ResearchFeb 18, 2021
February 2021 Malware Trends Report
This Februrary 2021 malware trends report is intended to help you better understand the evolving threat landscape and adapt your defenses accordingly.

Ben Zion Lavi
7 min read
-
 Data Security Security Bulletins
Data Security Security BulletinsFeb 09, 2021
What Federal Agencies Should Take Away from SolarWinds Attack
While patching, threat hunting, and remediation have been the focus of the SolarWinds attack, we can’t ignore the elephant in the room: stolen data.

Michael J. Wallace
4 min read
-
 Data Security
Data SecurityJan 29, 2021
What is DNS, How it Works + Vulnerabilities
What is DNS? It’s the address book of the internet. Read on to understand DNS, learn how you are vulnerable to attack through DNS, and how to protect your networks from DNS attacks.

Michael Buckbee
9 min read
-
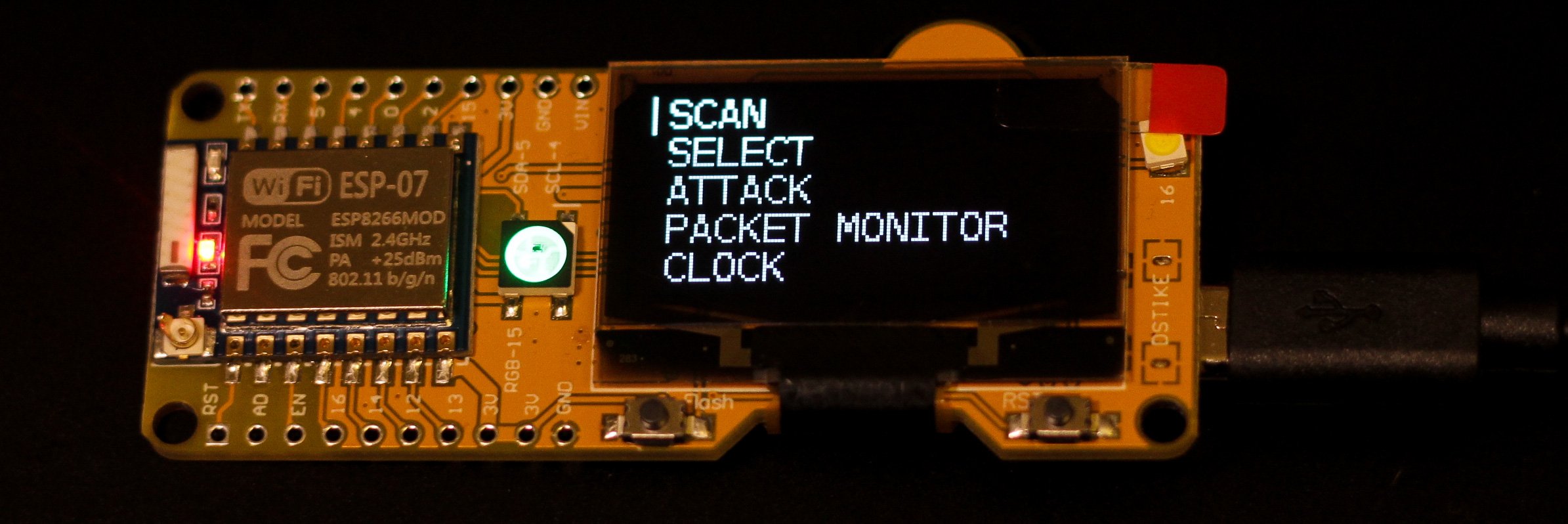 Data Security
Data SecurityJan 29, 2021
Hacking Wi-Fi With the ESP8266
Hack, monitor, and defend networks using the ESP8266 microcontroller and these Arduino based projects.

Kody Kinzie
4 min read
-
 Active Directory Data Security PowerShell
Active Directory Data Security PowerShellJan 29, 2021
Windows Management Instrumentation (WMI) Guide: Understanding WMI Attacks
WMI is a subsystem of PowerShell that can be used to monitor remote systems and users. In this guide, we’ll explain what WMI is, and how to use it.

Michael Buckbee
13 min read
-
 Data Security
Data SecurityJan 29, 2021
What Is Cryptojacking? Prevention and Detection Tips
Learn how cryptocurrency, cryptomining and cryptojacking work — also included are tips to prevent and detect cryptojacking before it's too late

Rob Sobers
8 min read
SECURITY STACK NEWSLETTER
Ready to see the #1 Data Security Platform in action?
Ready to see the #1 Data Security Platform in action?
“I was amazed by how quickly Varonis was able to classify data and uncover potential data exposures during the free assessment. It was truly eye-opening.”
Michael Smith, CISO, HKS
"What I like about Varonis is that they come from a data-centric place. Other products protect the infrastructure, but they do nothing to protect your most precious commodity — your data."
Deborah Haworth, Director of Information Security, Penguin Random House
“Varonis’ support is unprecedented, and their team continues to evolve and improve their products to align with the rapid pace of industry evolution.”
Al Faella, CTO, Prospect Capital