-
 Data Security
Data SecurityJun 24, 2022
Evil Twin Attack: What it is, How to Detect & Prevent it
The evil twin attack takes advantage of public WiFi connections. Learn how to prevent it from reaching you and your devices.

Josue Ledesma
5 min read
-
 Data Security
Data SecurityJun 16, 2022
What is Cyber Espionage? Complete Guide with Protection Tips
Cyber espionage is the unauthorized use of computer networks to access privileged information. Read on to learn more about this growing worldwide problem.

Robert Grimmick
11 min read
-
 Data Security
Data SecurityJun 15, 2022
Data Protection Guide: How To Secure Google Drive for Your Business
Does your company store, handle, or transmit confidential data in Google Drive? Learn about security, encryption, and data protection in Google Workspace.

David Harrington
7 min read
-
 Data Security
Data SecurityMay 20, 2022
82 Must-Know Data Breach Statistics [updated 2024]
These data breach statistics cover risk, cost, prevention and more — assess and analyze these stats to help prevent a data security incident.

Rob Sobers
11 min read
-
 Data Security
Data SecurityApr 12, 2022
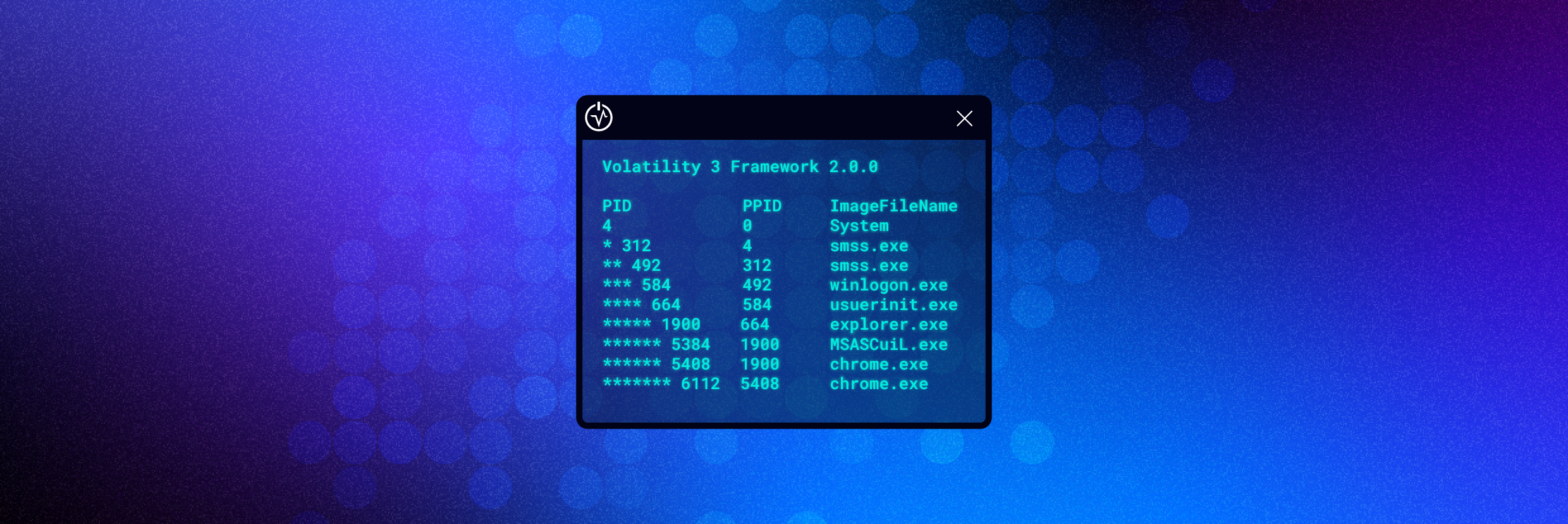
How to Use Volatility for Memory Forensics and Analysis
This article will cover what Volatility is, how to install Volatility, and most importantly how to use Volatility.

Neil Fox
8 min read
-
 Data Security
Data SecurityApr 07, 2022
CCSP vs. CISSP: Which One Should You Take?
Get an overview of the CCSP and CISSP exams and learn which certification is best for you and your career.

Josue Ledesma
5 min read
-
 Data Security
Data SecurityApr 06, 2022
Unpacking NIST Cybersecurity Framework 2.0
Learn how you can implement the NIST Cybersecurity Framework (CSF) 2.0 within your own organization and how Varonis helps.

Shawn Hays
8 min read
-
 Data Security
Data SecurityMar 31, 2022
Your Guide to Simulated Cyberattacks: What is Penetration Testing?
Penetration testing simulates a real-world cyber-attack on your critical data and systems. Here’s what penetration testing is, the processes and tools behind it, and how pen testing helps spot vulnerabilities before hackers do.

David Harrington
7 min read
-
 Data Security
Data SecurityMar 30, 2022
What is Terraform: Everything You Need to Know
Terraform is an infrastructure-as-code (IaC) solution that helps DevOps teams manage multi-cloud deployments. Learn about what is Terraform, the benefits of IaC, and how to get started.

David Harrington
5 min read
-
 Data Security
Data SecurityMar 21, 2022
How to Use Ghidra to Reverse Engineer Malware
An overview of the malware analysis tool Ghidra. This article covers how to install and navigate the Ghidra interface.

Neil Fox
7 min read
-
 Data Security
Data SecurityMar 18, 2022
What Is a Botnet? Definition and Prevention
Learn why botnets can be so dangerous and what your organization can do to protect your IoT devices and network.

Josue Ledesma
4 min read
-
 Data Security
Data SecurityFeb 25, 2022
Common Types of Malware
This piece covers the various types of malware that are available and their characteristics.

Neil Fox
7 min read
SECURITY STACK NEWSLETTER
Ready to see the #1 Data Security Platform in action?
Ready to see the #1 Data Security Platform in action?
“I was amazed by how quickly Varonis was able to classify data and uncover potential data exposures during the free assessment. It was truly eye-opening.”
Michael Smith, CISO, HKS
"What I like about Varonis is that they come from a data-centric place. Other products protect the infrastructure, but they do nothing to protect your most precious commodity — your data."
Deborah Haworth, Director of Information Security, Penguin Random House
“Varonis’ support is unprecedented, and their team continues to evolve and improve their products to align with the rapid pace of industry evolution.”
Al Faella, CTO, Prospect Capital