Featured Content

Data Security

Avia Navickas

Avia Navickas
Cloud Security

Yaki Faitelson
Data Security

Varonis Threat Labs
Data Security
-1.png)
Lexi Croisdale
-
 Data Security
Data SecurityAug 31, 2016
Malware Coding Lessons for IT People, Part II: Fun With FUD Ransomware!
Let’s not overthink ransomware! It’s just a small malicious piece of code with one devious goal — encrypting all of the user’s important files. It the unfortunate victim wants to...
Oded Awaskar
4 min read
-
 Privacy & Compliance
Privacy & ComplianceAug 23, 2016
HHS to Investigate Smaller HIPAA Privacy Breaches
As a reader of this blog, you know all about Health and Human Services’ (HHS) wall of shame. That’s where breaches involving protected health information (PHI) affecting 500 or more...

Michael Buckbee
1 min read
-
 Data Security
Data SecurityAug 19, 2016
New SamSam Ransomware Exploiting Old JBoss Vulnerability
One of the lessons learned from the uptick in ransomware attacks is that it pays to keep your security patches up to date. A few months ago the SamSam/Samas malware...

Michael Buckbee
1 min read
-
 Data Security
Data SecurityAug 17, 2016
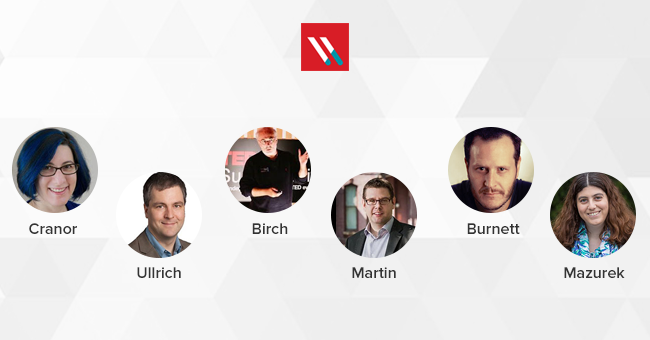
Six Authentication Experts You Should Follow
Our recent ebook shows what’s wrong with current password-based authentication technology. But luckily, there are a few leading experts that are shaping the future of the post-password world. Here are six people...

Michael Buckbee
3 min read
-
 Privacy & Compliance
Privacy & ComplianceAug 03, 2016
What is the Minimum Acceptable Risk Standards for Exchanges (MAR-E)?
Under the Affordable Care Act (ACA) of 2010, there are now online marketplaces to buy health insurance. These are essentially websites that allow consumers to shop around for an insurance...

Michael Buckbee
4 min read
-
 Data Security
Data SecurityAug 02, 2016
SQL Server Best Practices, Part I: Configuration
Am I the only one who finds the Microsoft SQL server best practice guides to be a little painful to trawl through? Somehow, I doubt it. After being frustrated reading...

Kieran Laffan
7 min read
-
 Privacy & Compliance
Privacy & ComplianceJul 27, 2016
Understanding Canada: Ontario’s New Medical Breach Notification Provision (and Other Canadian Data Privacy Facts)
Remember Canada’s profusion of data privacy laws? The Personal Information Protection and Electronic Documents Act (PIPEDA) is the law that covers all commercial organizations across Canada. Canadian federal government agencies,...

Michael Buckbee
1 min read
-
 Data Security
Data SecurityJul 27, 2016
21 Free Tools Every SysAdmin Should Know
Knowing the right tool to the right job is something that can save you hours of extra work and tedium. We’ve compiled a list of of some of the best...

Rob Sobers
4 min read
-
 Data Security
Data SecurityJul 21, 2016
Banks Secretly and Silently Struggling with Ransomware
“You’re almost certainly not going to hear about successful ransomware attacks on banks,” says Fraud Prevention Expert, Ross Hogan in an interview with Banking Exchange. “It is probably one of the...

Michael Buckbee
2 min read
-
 Data Security
Data SecurityJul 20, 2016
How to Identify Ransomware: Use Our New Identification Tool
Sadly, ransomware infections are routine enough that IT departments have started to develop standardized procedures for rapidly quarantining infected machines, determining the extent of damage and then attempting recovery operations.. For...

Michael Buckbee
1 min read
-
 Data Security
Data SecurityJul 19, 2016
How to Respond to a Cyber Security Incident
Every day another company is caught off guard by a data breach. While avoiding an attack is ideal, it’s not always possible. There’s no such thing as perfect security. Even...

Michael Buckbee
4 min read
-
 Privacy & Compliance
Privacy & ComplianceJul 19, 2016
Is Browsing Facebook While in the Hospital a HIPAA Violation?
A recently filed federal class-action suit claims that several healthcare providers are violating HIPAA’s rules on protected health information (PHI). If the suit succeeds, privacy advocates say it has the potential...

Michael Buckbee
2 min read
SECURITY STACK NEWSLETTER
Ready to see the #1 Data Security Platform in action?
Ready to see the #1 Data Security Platform in action?
“I was amazed by how quickly Varonis was able to classify data and uncover potential data exposures during the free assessment. It was truly eye-opening.”
Michael Smith, CISO, HKS
"What I like about Varonis is that they come from a data-centric place. Other products protect the infrastructure, but they do nothing to protect your most precious commodity — your data."
Deborah Haworth, Director of Information Security, Penguin Random House
“Varonis’ support is unprecedented, and their team continues to evolve and improve their products to align with the rapid pace of industry evolution.”
Al Faella, CTO, Prospect Capital