Featured Content

Data Security

Avia Navickas

Avia Navickas
Cloud Security

Yaki Faitelson
Data Security

Varonis Threat Labs
Data Security
-1.png)
Lexi Croisdale
-
 Active Directory
Active DirectoryApr 04, 2022
12 Group Policy Best Practices: Settings and Tips for Admins
Group Policy configures settings, behavior, and privileges for user and computers. In this article, you’ll learn best practices when working with Group Policy.

Jeff Brown
5 min read
-
 Data Security
Data SecurityMar 31, 2022
Your Guide to Simulated Cyberattacks: What is Penetration Testing?
Penetration testing simulates a real-world cyber-attack on your critical data and systems. Here’s what penetration testing is, the processes and tools behind it, and how pen testing helps spot vulnerabilities before hackers do.

David Harrington
7 min read
-
 Data Security
Data SecurityMar 30, 2022
What is Terraform: Everything You Need to Know
Terraform is an infrastructure-as-code (IaC) solution that helps DevOps teams manage multi-cloud deployments. Learn about what is Terraform, the benefits of IaC, and how to get started.

David Harrington
5 min read
-
 Threat Research
Threat ResearchMar 29, 2022
Defending Your Cloud Environment Against LAPSUS$-style Threats
Varonis breaks down the recent LAPSUS$ hacks and provides best practices for defending your cloud environment against LAPSUS$ style threats

Nathan Coppinger
6 min read
-
 Data Security
Data SecurityMar 21, 2022
How to Use Ghidra to Reverse Engineer Malware
An overview of the malware analysis tool Ghidra. This article covers how to install and navigate the Ghidra interface.

Neil Fox
7 min read
-
 Data Security
Data SecurityMar 18, 2022
What Is a Botnet? Definition and Prevention
Learn why botnets can be so dangerous and what your organization can do to protect your IoT devices and network.

Josue Ledesma
4 min read
-
 Threat Research
Threat ResearchMar 11, 2022
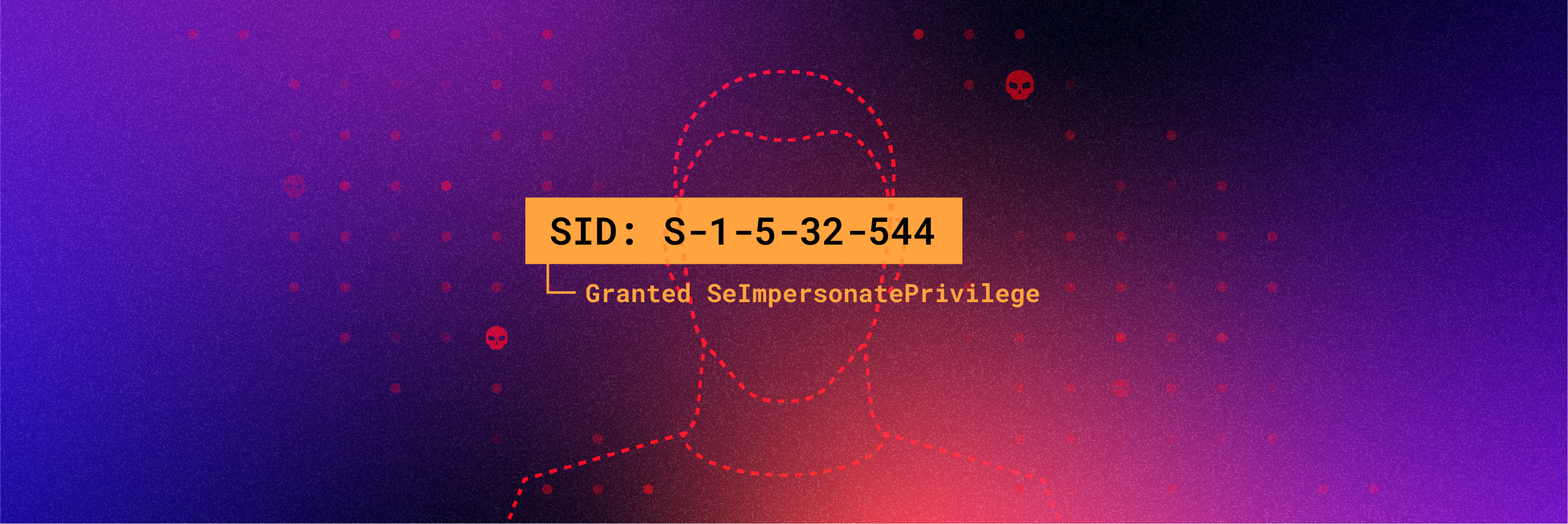
Is this SID taken? Varonis Threat Labs Discovers Synthetic SID Injection Attack
A technique where threat actors with existing high privileges can inject synthetic SIDs into an ACL creating backdoors and hidden permission grants.

Eric Saraga
3 min read
-
 Threat Research
Threat ResearchMar 04, 2022
ContiLeaks: Ransomware Gang Suffers Data Breach
Conti, a prolific ransomware group, has suffered a leak of both internal chat transcripts and source code being shared by a reported Ukrainian member

Jason Hill
6 min read
-
 Ransomware
RansomwareFeb 25, 2022
Ransomware-as-a-Service Explained: What is RaaS?
Ransomware as a service (RaaS) is an emerging and potent cybersecurity threat to all organizations. If you’re unaware of how RaaS works, your system is potentially at risk. What RaaS is and how to guard against it.

David Harrington
4 min read
-
 Data Security
Data SecurityFeb 25, 2022
Common Types of Malware
This piece covers the various types of malware that are available and their characteristics.

Neil Fox
7 min read
-
 Varonis Products
Varonis ProductsFeb 23, 2022
Varonis adds SSPM functionality to DatAdvantage Cloud
SaaS misconfigurations can unintentionally expose valuable corporate data. The new Insights Dashboard from Varonis helps you find and fix these security gaps.

Avia Navickas
2 min read
-
 Data Security
Data SecurityFeb 10, 2022
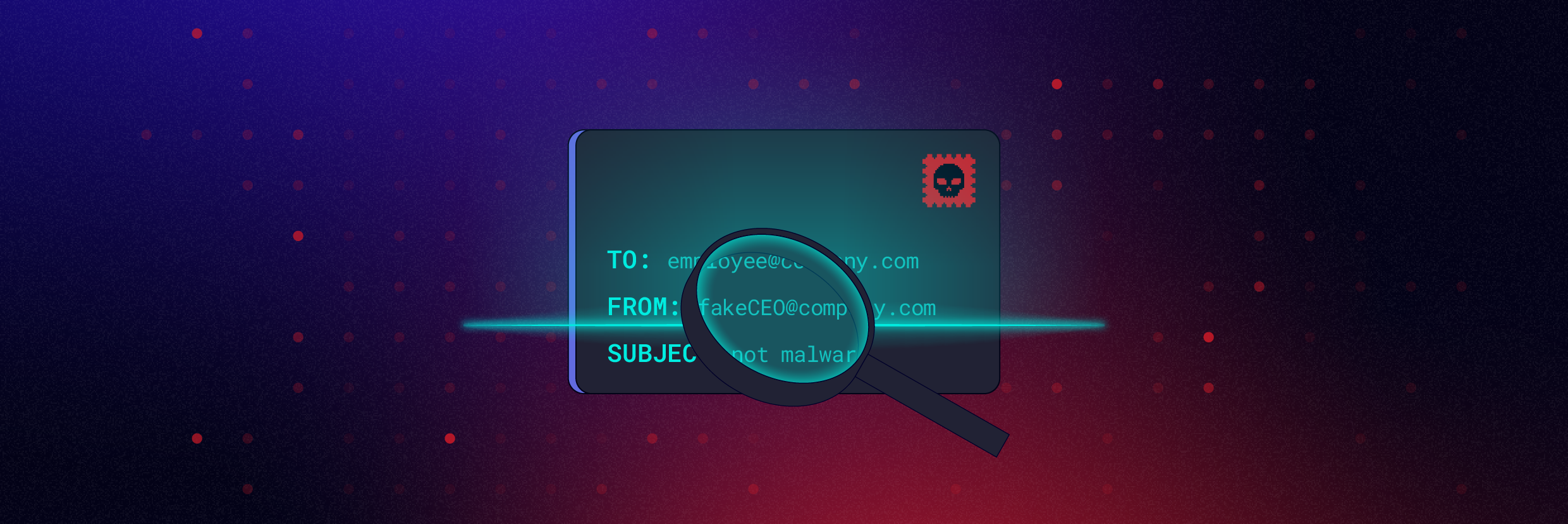
Identify and Investigate Business Email Compromise (BEC) Scams
In this post, we'll review how to spot Business Email Compromise Scams and walk you through an investigation with Varonis.

Ed Lin
9 min read
SECURITY STACK NEWSLETTER
Ready to see the #1 Data Security Platform in action?
Ready to see the #1 Data Security Platform in action?
“I was amazed by how quickly Varonis was able to classify data and uncover potential data exposures during the free assessment. It was truly eye-opening.”
Michael Smith, CISO, HKS
"What I like about Varonis is that they come from a data-centric place. Other products protect the infrastructure, but they do nothing to protect your most precious commodity — your data."
Deborah Haworth, Director of Information Security, Penguin Random House
“Varonis’ support is unprecedented, and their team continues to evolve and improve their products to align with the rapid pace of industry evolution.”
Al Faella, CTO, Prospect Capital