Organizations are continuing to invest in Microsoft Azure, with Microsoft reporting 21% growth in their server products and cloud services in Q2 FY2025. There are multiple drivers for the trend in cloud adoption, including AI, but there continues to be a single driver for the majority of cloud breaches: identity risk.
An extremely complicated web develops over time at many enterprise organizations as a result of new Azure subscriptions, resources, and resource groups being added year over year and month over month. Also, this organic growth is compounded by the acquisition of other businesses and the acquired data estates grafted into the parent company.

One primary way to manage the plethora of role combinations and scope entitlements is through role-based access control (RBAC). However, managing RBAC in the Azure portal can be tedious and impossible to scale. As a result, organizations consistently report that scoping and access assignments go dormant or stale over time - collecting dust and cobwebs.
Introducing the Azure Access Graph
Varonis continues its investment in Azure access and entitlement management by adding the Azure Access Graph to its industry-leading Data Security Platform (DSP) with the following features.
- Analyze effective access by understanding which roles, groups, scoping policies, and resource policies affect access.
- Prevent data exposure by identifying policies that expose sensitive data publicly.
- Clean up stale privileges that can be exploited by identifying inactivity
- Visualize the containers and various resources that a single identity can access
Like Varonis for AWS, security teams can easily understand how users, roles, groups, and policies map to data. This information then informs teams how to block access paths and reduce exposure.
Visualize effective data access.
With the retirement of Entra Permissions Management, organizations are looking for Cloud Infrastructure Entitlement Management (CIEM) capabilities from their DSP to detect, monitor, and adjust unused and excessive permissions in Azure for least privilege. Varonis’ Azure Access Graph and many other features in the platform can fill these gaps.
As shown in the snapshot below, the Varonis access graph provides a simplified view of the identities and service principals that can access a resource, along with the ability to explore the origins of their permissions.
Rather than clicking through dozens of roles, role assignments, and inherited scopes in the Azure portal or using PowerShell – the access graph simplifies the investigation process. Users can simply zoom into each connected element to find overexposure and access pathways.
Explore the bidirectional data access flow between identities, roles, and resources in Azure
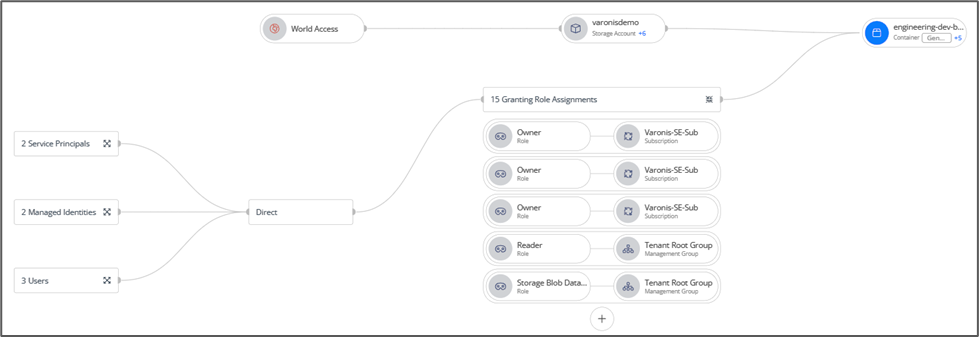
Explore the bidirectional data access flow between identities, roles, and resources in Azure
The access graph is adaptive to changes in the environment to give security and cloud teams the latest vantage point. This is critical when organizations uncover a potential compromised user or suspect a threat, as they can easily see all of the resources that a particular account has access to.
Improve security posture.
Organizations struggle to manage privileges and entitlements that are constantly evolving. Finding excessive or outdated privileges can be a challenge. The access graph intuitively enables admins to open an identity card to glean important details like whether or not the identity is inactive or stale, along with further information about that identity’s assignments elsewhere.
Investigate Azure accounts and relevant details in the identity card directly from the access graph
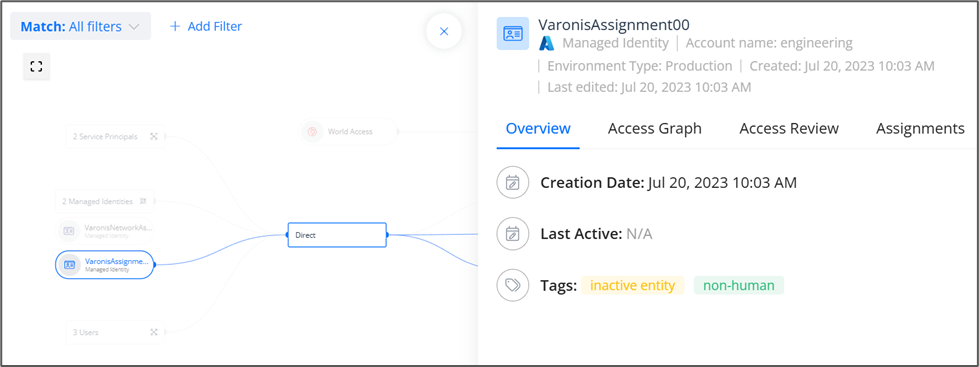
Investigate Azure accounts and relevant details in the identity card directly from the access graph
From the access graph, users can also explore other dashboards and lists in the Varonis platform to prioritize posture remediation efforts across the estate. Data-driven insights are one of the key attributes of a healthy cloud governance program. Therefore, Varonis continuously researches threats to fine-tune how data risks are represented in the platform and bring vital issues to the surface.

Varonis for Azure further enables teams to take data-driven action on the account and/or the resource by blocking public access to Azure storage containers, disabling blob anonymous access on storage accounts, disabling stale Azure users, and more.
Varonis has your back and your cloud.
Several acquisitions have already occurred in 2025 within the multi-cloud security industry, and some services are reaching end of support. Meanwhile, Varonis is accelerating its support of multi-cloud customers in Azure and elsewhere. The platform has expanded to cover Azure Databases, and Varonis recently acquired an innovative Database Access Monitoring (DAM) company delivering real-time monitoring and just-in-time authorization policies across on-prem and cloud data sources.
This investment doesn’t stop with Microsoft Azure. Amazon Redshift, MongoDB, MySQL, PostgreSQL, Google Workspace, Google Cloud, Salesforce, Box, UNIX/LINUX, and ServiceNow are among a growing list of other cloud sources that Varonis actively protects data in today. Securing data is the mission, no matter the cloud.
What should I do now?
Below are three ways you can continue your journey to reduce data risk at your company:
Schedule a demo with us to see Varonis in action. We'll personalize the session to your org's data security needs and answer any questions.
See a sample of our Data Risk Assessment and learn the risks that could be lingering in your environment. Varonis' DRA is completely free and offers a clear path to automated remediation.
Follow us on LinkedIn, YouTube, and X (Twitter) for bite-sized insights on all things data security, including DSPM, threat detection, AI security, and more.









.jpg)