
Michael Buckbee
Michael has worked as a sysadmin and software developer for Silicon Valley startups, the US Navy, and everything in between.
-
 Data Security
Data SecuritySep 30, 2019
A Practical Software Approach to Insider Threats
Insider data theft presents multiple challenges for traditional IT security. Insiders are employees who are entitled to be in the network unlike hackers. Standard perimeter security measures won’t work. But...

Michael Buckbee
5 min read
-
 Data Security
Data SecurityJul 09, 2019
Adventures in Fileless Malware, Part IV: DDE and Word Fields
For this next post, I was all ready to dive into a more complicated fileless attack scenario involving multiple stages and persistence. Then I came across an incredibly simple code-free...

Michael Buckbee
4 min read
-
 Data Security
Data SecurityJun 20, 2019
Working With Windows Local Administrator Accounts, Part III
One point to keep in mind in this series is that we’re trying to limit the powers that are inherent in Administrator accounts. In short: use the Force sparingly. In...

Michael Buckbee
2 min read
-
 Data Security
Data SecurityNov 05, 2018
California Consumer Privacy Act (CCPA) vs. GDPR
Check out our interactive Venn diagram below to better understand the similarities and differences between the GDPR and CCPA.

Michael Buckbee
5 min read
-
 Data Security
Data SecurityOct 10, 2018
What is ITAR Compliance? Definition and Regulations
Learn more about ITAR compliance, requirements, and penalties. Find the definition, detail of regulations, types of defense articles, and more from Varonis.

Michael Buckbee
4 min read
-
 Data Security
Data SecurityOct 05, 2018
Master Fileless Malware Penetration Testing!
Our five-part series brings you up to speed on stealthy techniques used by hackers. Learn how to sneakily run scripts with mshta, rundll32, and regsrvr32, scary Windows binaries that live...

Michael Buckbee
1 min read
-
 Data Security
Data SecurityAug 31, 2018
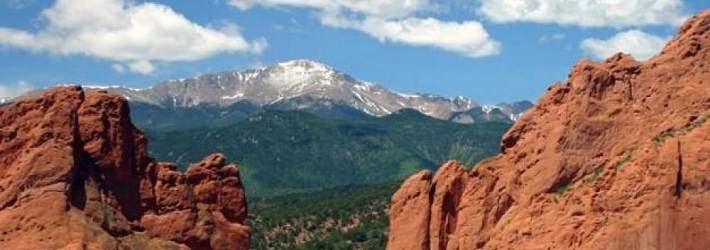
What is the Colorado Privacy Law?
On September 1, 2018, the Colorado Protections for Consumer Data Privacy law, HB 18-1128, goes into effect. A bi-partisan group introduced HB 18-1128 in January, and after the usual negotiations,...

Michael Buckbee
2 min read
-
 Data Security
Data SecurityJul 19, 2018
The Malware Hiding in Your Windows System32 Folder: More Rundll32 and LoL Security Defense Tips
When we left off last, I showed how it’s possible to run VBScript directly from mshta. I can play a similar trick with another LoL-ware binary, our old friend rundll32....

Michael Buckbee
3 min read
-
 Data Security
Data SecurityJul 02, 2018
The Malware Hiding in Your Windows System32 Folder: More Alternate Data Streams and Rundll32
Last time, we saw how sneaky hackers can copy malware into the Alternate Data Stream (ADS) associated with a Windows file. I showed how this can be done with the...

Michael Buckbee
4 min read
-
 Data Security
Data SecurityJun 14, 2018
The Malware Hiding in Your Windows System32 Folder: Certutil and Alternate Data Streams
We don’t like to think that the core Window binaries on our servers are disguised malware, but it’s not such a strange idea. OS tools such as regsrv32 and mshta...

Michael Buckbee
3 min read
-
Data Security
Jun 04, 2018
The Malware Hiding in Your Windows System32 Folder: Mshta, HTA, and Ransomware
The LoL approach to hacking is a lot like the “travel light” philosophy for tourists. Don’t bring anything to your destination that you can’t find or inexpensively purchase once you’re…

Michael Buckbee
5 min read
-
 Data Security
Data SecurityJun 01, 2018
The State of CryptoWall in 2018
CryptoWall and its variants are still favorite toys of the cybercriminals that want your Bitcoin. Learn more about the state of CryptoWall in 2018, today!

Michael Buckbee
5 min read
SECURITY STACK NEWSLETTER
Ready to see the #1 Data Security Platform in action?
Ready to see the #1 Data Security Platform in action?
“I was amazed by how quickly Varonis was able to classify data and uncover potential data exposures during the free assessment. It was truly eye-opening.”
Michael Smith, CISO, HKS
"What I like about Varonis is that they come from a data-centric place. Other products protect the infrastructure, but they do nothing to protect your most precious commodity — your data."
Deborah Haworth, Director of Information Security, Penguin Random House
“Varonis’ support is unprecedented, and their team continues to evolve and improve their products to align with the rapid pace of industry evolution.”
Al Faella, CTO, Prospect Capital