
Michael Buckbee
Michael has worked as a sysadmin and software developer for Silicon Valley startups, the US Navy, and everything in between.
-
 Data Security
Data SecurityMar 29, 2020
Varonis Named a ‘Strong Performer’ in 2019 Forrester Wave for Data Security Portfolio Vendors
Varonis has been singled out by Forrester as one of “the 13 providers who matter most” of data security vendors in their Forrester Wave™: Data Security Portfolio Vendors, Q2 2019....

Michael Buckbee
1 min read
-
 Data Security
Data SecurityMar 29, 2020
What is a DDoS Attack? Identifying Denial-of-Service Attacks
Distributed Denial-of-service (DDoS) attacks are disruptive and costly. Learn more about DDoS attacks and how you can better protect your network.

Michael Buckbee
6 min read
-
 Data Security
Data SecurityMar 29, 2020
Varonis Gets Lightning Fast with Solr
Any security practitioner that has had to perform forensic analysis on a cybersecurity incident likely describes the process as “searching for a needle in a stack of needles.” Even Tony...

Michael Buckbee
2 min read
-
 Data Security
Data SecurityMar 29, 2020
Browsing Anonymously: Is It Really Anonymous?
What can tools like private browsing and VPNs really deliver in terms of privacy? See for yourself as we take a deep dive into popular privacy tools

Michael Buckbee
5 min read
-
 Active Directory
Active DirectoryMar 29, 2020
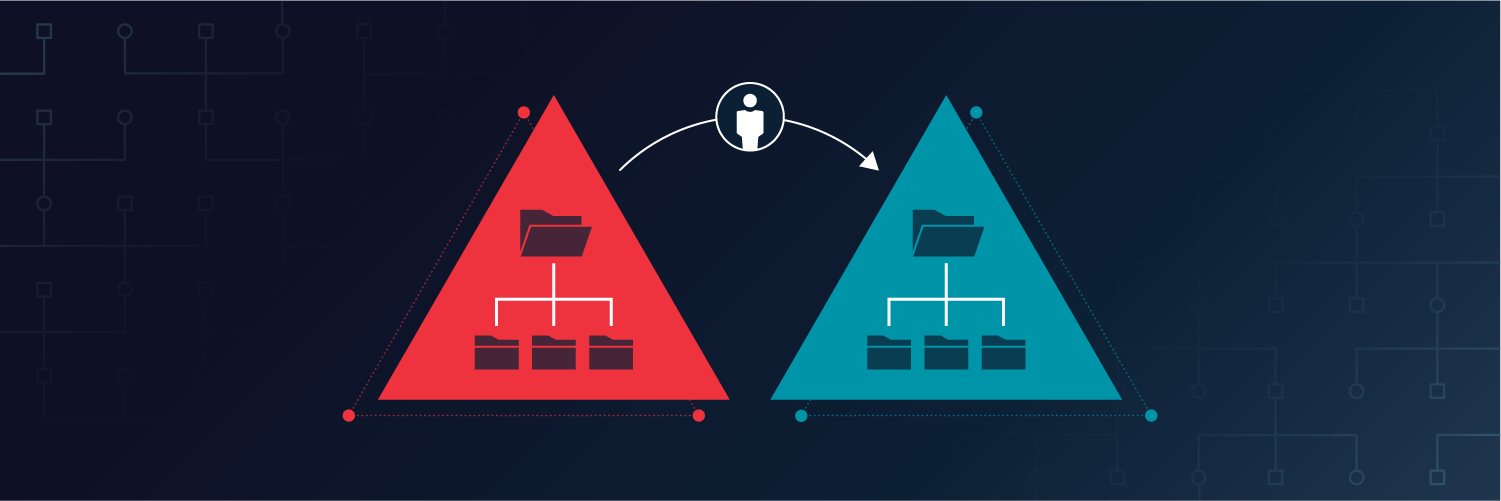
Active Directory Migration Tool (ADMT): Your Essential Guide
The Active Directory Migration Tool is a Microsoft tool that makes it easy to move AD objects to other domains or forests. Read on to learn how to use ADMT.

Michael Buckbee
5 min read
-
 Data Security
Data SecurityMar 29, 2020
Security Risk Analysis Is Different From Risk Assessment
At the Inside Out Security blog, we’re always preaching the importance of risk assessments. IT and the C-levels need to evaluate vulnerabilities in their corporate systems to determine risk factors....

Michael Buckbee
4 min read
-
 Data Security
Data SecurityMar 29, 2020
Analyzing Company Reputation After a Data Breach
Does a data breach affect how your customers see you? Take a look at what Americans think as we dive into the relationship between breaches and reputation.

Michael Buckbee
9 min read
-
 Data Security
Data SecurityMar 29, 2020
What Would The World’s Data Look Like if it Were Physical?
Before we start to understand how to properly manage our data, we need to understand just how much there is to manage! Take a look at these analogies and visual aides to get a better idea of the size of our data.

Michael Buckbee
1 min read
-
 Data Security
Data SecurityMar 29, 2020
Why A Honeypot Is Not A Comprehensive Security Solution
A core security principle and perhaps one of the most important lessons you’ll learn as a security pro is AHAT, “always have an audit trail”. Why? If you’re ever faced...

Michael Buckbee
5 min read
-
 Data Security
Data SecurityMar 29, 2020
What is Metasploit? The Beginner's Guide
This Ruby-based open-source framework, Metasploit, allows testing via command line alterations or GUI. Learn more with our beginner's guide today.

Michael Buckbee
6 min read
-
 Data Security PowerShell Security Bulletins
Data Security PowerShell Security BulletinsOct 17, 2019
What is Endpoint Security? A Complete Guide
Endpoint security is a growing concern for enterprises in every industry, given the value of digital assets and data, and must be a cybersecurity priority.

Michael Buckbee
7 min read
-
 Data Security Security Bulletins
Data Security Security BulletinsOct 02, 2019
What is a Security Operations Center (SOC)?
Learn how a security operations center (SOC) functions in an enterprise, SOC models, job roles, best practices and the value it brings to an organization

Michael Buckbee
7 min read
SECURITY STACK NEWSLETTER
Ready to see the #1 Data Security Platform in action?
Ready to see the #1 Data Security Platform in action?
“I was amazed by how quickly Varonis was able to classify data and uncover potential data exposures during the free assessment. It was truly eye-opening.”
Michael Smith, CISO, HKS
"What I like about Varonis is that they come from a data-centric place. Other products protect the infrastructure, but they do nothing to protect your most precious commodity — your data."
Deborah Haworth, Director of Information Security, Penguin Random House
“Varonis’ support is unprecedented, and their team continues to evolve and improve their products to align with the rapid pace of industry evolution.”
Al Faella, CTO, Prospect Capital