
Michael Buckbee
Michael has worked as a sysadmin and software developer for Silicon Valley startups, the US Navy, and everything in between.
-
 Data Security
Data SecurityMar 29, 2020
Zero-Day Vulnerability Explained
Find out how zero-day vulnerabilities become zero-day exploits and zero-day attacks, and how to defend your network from zero-day attacks and exploits.

Michael Buckbee
3 min read
-
 Data Security
Data SecurityMar 29, 2020
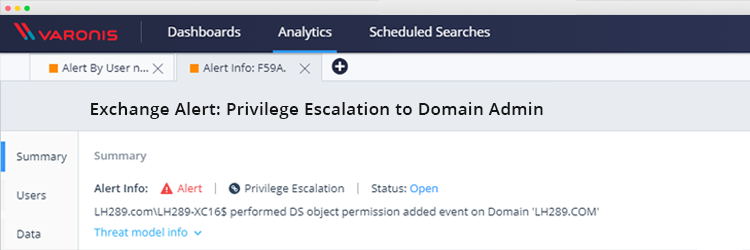
Exchange Vulnerability: How to Detect Domain Admin Privilege Escalation
Researchers recently uncovered a vulnerability in Exchange that allows any domain user to obtain Domain admin privileges that allow them to compromise AD and connected hosts. Here’s how the attack...

Michael Buckbee
1 min read
-
 Privacy & Compliance
Privacy & ComplianceMar 29, 2020
What the H**L Does Reasonable Data Security Really Mean?
For anyone who’s spent time looking at data security laws and regulations, you can’t help but come across the words “reasonable security”, or its close cousin “appropriate security”. You can...

Michael Buckbee
3 min read
-
 Privacy & Compliance
Privacy & ComplianceMar 29, 2020
Post-Davos Thoughts on the EU NIS Directive
I’ve been meaning to read the 80-page report published by the World Economic Forum (WEF) on the global risks humankind now faces. They’re the same folks who bring you the once...

Michael Buckbee
3 min read
-
 Active Directory
Active DirectoryMar 29, 2020
Active Directory Domain Controller (AD DC) Could Not Be Contacted [SOLVED]
Sometimes clients report an error “An Active Directory Domain Controller (AD DC) for the domain could not be contacted.” Read on to learn how to troubleshoot and resolve this issue.

Michael Buckbee
2 min read
-
 Data Security
Data SecurityMar 29, 2020
Maximize your ROI: Maintaining a Least Privilege Model
TL;DR: Managing permissions can be expensive. For a 1,000 employee company, the overhead of permissions request tickets can cost up to $180K/year. Automating access control with DataPrivilege can save $105K/year...

Michael Buckbee
5 min read
-
Mar 29, 2020
Varonis Version 7 Highlights
Varonis Version 7 is now generally available – check out our latest 7.4 release and see some of the highlights of what’s new. 25 new widgets to manage and protect...

Michael Buckbee
1 min read
-
 PowerShell
PowerShellMar 29, 2020
How To Use PowerShell for Privilege Escalation with Local Computer Accounts
Privilege escalation is when an attacker is able to exploit the current rights of an account to gain additional, unexpected access. While this can be caused by zero-day vulnerabilities, state-level...

Michael Buckbee
3 min read
-
 Privacy & Compliance
Privacy & ComplianceMar 29, 2020
GDPR: The Right to Be Forgotten and AI
One (of the many) confusing aspects of the EU General Data Protection Regulation (GDPR) is its “right to be forgotten”. It’s related to the right to erasure but takes in far...

Michael Buckbee
3 min read
-
 Privacy & Compliance
Privacy & ComplianceMar 29, 2020
NYDFS Cybersecurity Regulation in Plain English
Learn about the new NYDFS cybersecurity regulation and the rules for basic principles of data security, documentation of security policies, and much more.

Michael Buckbee
5 min read
-
 Data Security
Data SecurityMar 29, 2020
12 Ways Varonis Helps You Manage Mergers and Acquisitions
A well-constructed Merger & Acquisition (M&A) playbook reduces the overall time, cost and risk of the upcoming merger and/or acquisition. Gartner advises that organizations who intend to grow through acquisitions...

Michael Buckbee
6 min read
-
 Data Security
Data SecurityMar 29, 2020
CISM vs. CISSP Certification: Which One is Best for You?
CISM and CISSP are two of the most highly regarded certifications for cybersecurity leaders and practitioners, but their requirements aren’t trivial. Both require a significant investment of time and money – so It’s important to determine which is right for you. Take a look at our comparison of the two to learn more.

Michael Buckbee
3 min read
SECURITY STACK NEWSLETTER
Ready to see the #1 Data Security Platform in action?
Ready to see the #1 Data Security Platform in action?
“I was amazed by how quickly Varonis was able to classify data and uncover potential data exposures during the free assessment. It was truly eye-opening.”
Michael Smith, CISO, HKS
"What I like about Varonis is that they come from a data-centric place. Other products protect the infrastructure, but they do nothing to protect your most precious commodity — your data."
Deborah Haworth, Director of Information Security, Penguin Random House
“Varonis’ support is unprecedented, and their team continues to evolve and improve their products to align with the rapid pace of industry evolution.”
Al Faella, CTO, Prospect Capital