
Michael Buckbee
Michael has worked as a sysadmin and software developer for Silicon Valley startups, the US Navy, and everything in between.
-
 Data Security
Data SecurityMar 29, 2020
Ponemon and NetDiligence Remind Us Data Breach Costs Can Be Huuuge!
Those of us in the infosec community eagerly await the publication of Ponemon’s annual breach cost analysis in the early summer months. What would summer be without scrolling through the...

Michael Buckbee
4 min read
-
 Privacy & Compliance
Privacy & ComplianceMar 29, 2020
What is FISMA Compliance? Regulations and Requirements
FISMA is the federal government’s security requirements. If you work for on with a federal agency read on to learn how to get (and stay) compliant.

Michael Buckbee
3 min read
-
 Data Security
Data SecurityMar 29, 2020
Practical Cyber Threat Cost Analysis: A Risk Model for Denial of Service Attacks
Risk analysis doesn’t get the attention it deserves. It’s the part of the risk assessment process where you feed all your important results — where the credit cards numbers are...

Michael Buckbee
5 min read
-
 Data Security
Data SecurityMar 29, 2020
Kerberos Authentication Explained
Learn more about Kerberos Authentication, the widely-used authorization technology. Contact us today to learn how Varonis monitors Kerberos, and more.

Michael Buckbee
4 min read
-
 Data Security
Data SecurityMar 29, 2020
The Difference Between E3 and E5 Office365 Features
Microsoft’s Enterprise Mobility and Security offerings are additional sets of security services that can be purchased to help control, audit and protect the data and users of Microsoft’s Azure and...

Michael Buckbee
3 min read
-
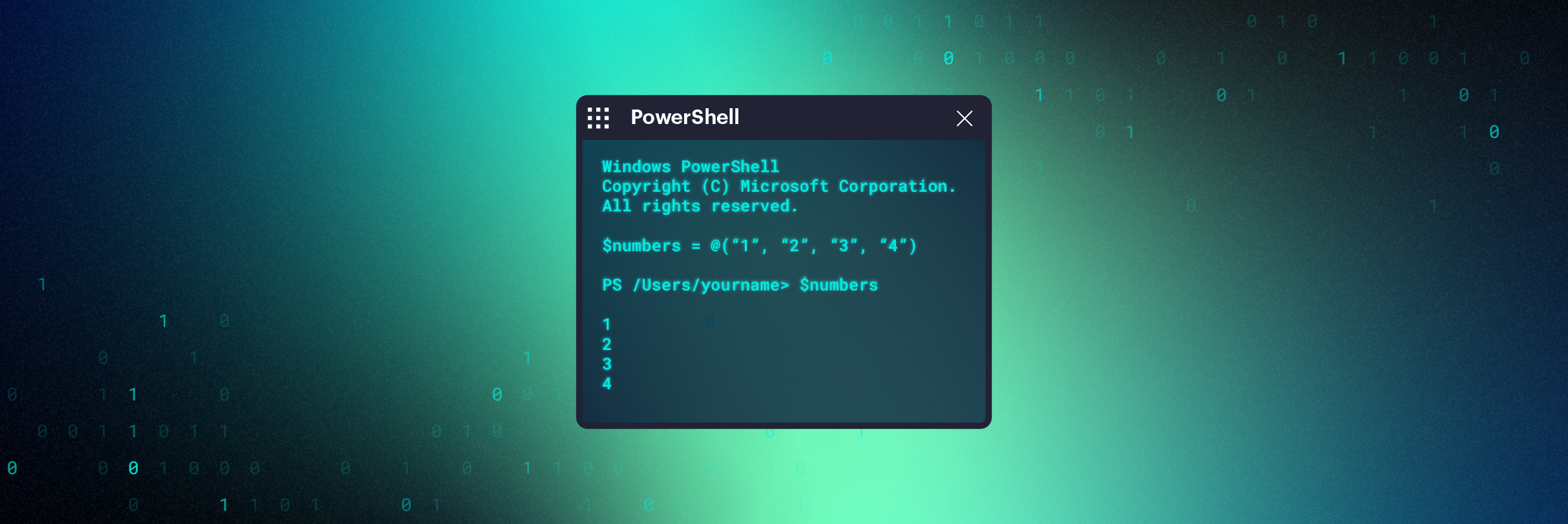 PowerShell
PowerShellMar 29, 2020
PowerShell Array Guide: How to Use and Create
Learn how to best use PowerShell arrays — we'll cover the basics of how to create them, work with them as well as some more advanced techniques.

Michael Buckbee
10 min read
-
 Data Security PowerShell
Data Security PowerShellMar 29, 2020
PowerShell Obfuscation: Stealth Through Confusion, Part II
Let’s step back a little from the last post’s exercise in jumbling PowerShell commands. Obfuscating code as a technique to avoid detection by malware and virus scanners (or prevent reverse...

Michael Buckbee
3 min read
-
 Data Security
Data SecurityMar 29, 2020
Data Security 2017: We’re All Hacked
Remember more innocent times back in early 2017? Before Petya, WannaCry, leaked NSA vulnerabilities, Equifax, and Uber, the state of data security was anything but rosy, but I suppose there...

Michael Buckbee
4 min read
-
 Data Security
Data SecurityMar 29, 2020
A Guide on the Data Lifecycle: Identifying Where Your Data is Vulnerable
Data is a company’s most valuable asset. To maintain data’s value, it’s vital to identify where that data is vulnerable. According to data and ethics expert Dr. Gemma Galdon Clavell,...

Michael Buckbee
6 min read
-
 Data Security
Data SecurityMar 29, 2020
Solving The Cybersecurity Skills Shortage Within Your Organization
As technology evolves and cyberattacks increase so does the gap in the cybersecurity workforce, read on to see tech shortage solutions for your business

Michael Buckbee
3 min read
-
 Data Security Security Bulletins
Data Security Security BulletinsMar 29, 2020
Varonis DatAlert and IBM QRadar
Varonis now integrates with the IBM QRadar Security Intelligence Platform, with the Varonis App for QRadar. The Varonis App for QRadar adds context and security analytics to simplify investigations, streamline threat detection, and build...

Michael Buckbee
1 min read
-
 Security Bulletins
Security BulletinsMar 29, 2020
Data Classification Labels: Integrating with Microsoft Information Protection (MIP)
We’re thrilled to announce the beta release of Data Classification Labels: integrating with Microsoft Information Protection (MIP) to enable users to better track and secure sensitive files across enterprise data...

Michael Buckbee
1 min read
SECURITY STACK NEWSLETTER
Ready to see the #1 Data Security Platform in action?
Ready to see the #1 Data Security Platform in action?
“I was amazed by how quickly Varonis was able to classify data and uncover potential data exposures during the free assessment. It was truly eye-opening.”
Michael Smith, CISO, HKS
"What I like about Varonis is that they come from a data-centric place. Other products protect the infrastructure, but they do nothing to protect your most precious commodity — your data."
Deborah Haworth, Director of Information Security, Penguin Random House
“Varonis’ support is unprecedented, and their team continues to evolve and improve their products to align with the rapid pace of industry evolution.”
Al Faella, CTO, Prospect Capital